As organizations increasingly adopt containers for faster and more scalable application deployment, ensuring their security has become a top priority. This is where Container Scanning Tools play a critical role. These tools are designed to analyze container images and identify vulnerabilities, misconfigurations, and outdated dependencies before they reach production environments. By integrating scanning into the development pipeline, teams can detect security risks early and maintain compliance with industry standards.
Modern solutions go beyond basic vulnerability detection by offering continuous monitoring, automated alerts, and detailed remediation guidance. They also support popular container platforms like Docker and Kubernetes, making them essential for DevSecOps practices. With cyber threats evolving rapidly, businesses must proactively secure their containerized applications. Implementing reliable scanning solutions not only reduces risk but also strengthens overall application integrity and trust in cloud-native environments.
What Are Container Scanning Tools?
Container scanning software are security tools that scan container images, lightweight, movable images in the form of applications with their dependencies and runtime settings, and which are analyzed with respect to vulnerabilities, misconfigurations, and any other security threat to be deployed. They operate by matching pictures to layers, comparing components, such as base pictures, libraries, and packages, with databases, such as the National Vulnerability Database (NVD) or CVE lists, and also diagnosing issues, such as out-of-date software, secrets being revealed, or nonconforming settings.
Many types of test tools (e.g., Trivy, Snyk,k or Aqua) are frequently included in CI/CD pipelines to execute some form of a shift-left security, including a scan of the repository as part of a build, and provide reports on remediation suggestions to help prevent exploits in production of Kubernetes or Docker applications.
Benefits of Container Scanning Tools
Container scanning devices enhance the security of a containerized environment since they point out vulnerabilities at an earlier stage. They are quite appropriate in proactive risk management and DevOps processes.
Key Benefits
- Identify known vulnerabilities in containers, packages, and dependencies on rest, and minimize the risks of breach.
- Enforce regulatory compliance (e.g., HIPAA, SOC 2) through automated tools and audit reports.
- carry out security scanning of CI/CD pipelines, verification that safe images are deployed only, and shift-left security is acceptable.
- Remediation and prioritization to do remediation and prioritization faster, trace problems to specific layers or packages.
- Allow real-time monitoring to detect drifts and threats to the production process.
- Increase the visibility of security posture by creating SBOM, enforcing policies, and providing real-time notifications.
- Optimize operations through the minimization of manual operations and downtimes through automated remedies.
List of 12 Best Container Scanning Tools
1. Trivy
Website:https://trivy.dev
Trivy is an open-source security scanner project of Aqua Security that is utilized to locate vulnerabilities, misconfigurations, secrets, and generate SBOMs (Software Bill of Materials) in container images, filesystems, Kubernetes clusters, Git repositories, Infrastructure as Code (IaC), and cloud configurations.
It is an expeditious and plain single-binary CLI tool that can be effortlessly incorporated into CI/CD pipelines, local development processes, or a pre-commit hook, and a regularly updated vulnerability database to provide an all-inclusive scan on packages across various package ecosystems. It has a number of supported output formats, including JSON, SARIF, and GitHub annotations, and capabilities, including policy enforcement.
Key features:
- Images Scans filesystems, VM images, remote Git repositories, Kubernetes, and AWS environments.
- Identifies known OS packages and applications dependencies vulnerabilities (CVEs).
- Detects the misconfigurations in infrastructure-as-code and leaked secrets (passwords, keys, tokens).
- Creates and authenticates SPDX and CycloneDX formats of SBOMs.
- Cooperates with license-compliance scanning to indicate potentially dangerous licenses like AGPL or proprietary licenses.
- Simple integration of CI/CD through CLI, Docker, K8s operators, and cloud workflows.
Pros:
- Free & open source
- Fast and lightweight CLI
- All-in-one (vulnerabilities, secrets, misconfigs, SBOM)
- Easy CI/CD integration
Cons:
- No GUI (CLI only)
- Limited enterprise features
- Possible false positives
Pricing
- Trivy is free and open source (no license cost).
2. Clair
Website:https://clairproject.org/
Clair is an open-source vulnerability scanner based on static analysis designed by CoreOS (since acquired by Red Hat) to scan vulnerabilities in container images, including those in Docker and OCI formats. It operates by indexing image layers to find packages, runtimes, and distributions, and comparing them with vulnerability databases provided by various sources such as Debian, Alpine, Red Hat, and the NVD to create reports showing CVEs with severity scores.
Container scanning tools It is an API-based design, which allows easy integration into CI/CD pipelines, container registries such as Quay.io, and registries, and supports incremental scans without re-indexing unchanged layers.
Key Features
- Uses parses OCI and Docker image layers to detect vulnerabilities on a layer-by-layer basis.
- Compares packages to vulnerability information of 9+ Linux distros and NVD.
- Indexing/matching pipeline re-evaluable fast scans on new CVEs.
- Easy integration with registries (e.g., Quay.io) and CI systems through API.
- Changes to layers incrementally. Only change scanning; it works with a variety of image formats.
- Apache is a licensed open-source and community-maintained CVE.
Pros:
- Deep layer-based scanning
- Strong integration with container registries
- Incremental scanning improves speed
Cons:
- Setup is complex
- Slower than modern tools
- Limited features beyond vulnerability scanning
Pricing:
- Free:$0 per user/month
- Team:$4USD per user/month
- Enterprise:$21USD per user/month
3. Anchore Engine / Anchore Enterprise
Website:anchore.com.
Anchore Engine is a container image scanning engine that is open-source and offers in-depth inspection, source vulnerability analysis, and policy enforcement of containerized applications. The basis of Anchore Enterprise is a trading platform with a more advanced mechanism, such as a user interface, scalable workflows, and professional DevSecOps integrations that allow security scanning, SBOM creation, compliance checking of CI/CD pipelines and registries, and even integration with malware removal tools to detect and remediate malicious code effectively.
Key Features
- Scanning of container images to detect vulnerabilities and malware, as well as configuration.
- Severity-based vulnerability assessment and recommendations on remediation, along with the affected packages.
- Checks with standards, such as CIS Docker Benchmark and NIST 800-190.
- Component Model for creating security and organization rules.
- Software composition visibility, SBOM generation, and analysis.
- API, CLI, integrations with CI/CD tools, registries,s and Kubernetes.
- Air-gapped deployment support and support of a large-scale environment (Enterprise).
Pros:
- Strong policy enforcement
- Detailed vulnerability analysis
- SBOM and compliance support
Cons:
- Complex setup
- Enterprise features are paid
- Slower scanning compared to lightweight tools
Pricing
- Anchore Enterprise is priced as a subscription and tailored to the scale of workload, type of deployment, and support requirements- contact sales to get quotes because public pricing is not provided.
4. Falco
Website:https://falco.org
Falco is an open-source, cloud-native, runtime security engine that is primarily used to identify abnormal behavior and potential threats in a containerized system, such as Kubernetes, hosts, cloud management platforms, container scanning tools, and not on the more traditional image-based scanning. It captures system calls, kernel events, and other flows of information (typically via the eBPF) in real-time, processes them using programmable rules to issue alerts about things like privilege escalations, crypto mining, or file exfiltrations, and adds event metadata on those events with the various container runtimes.
Key Features
- Detecting Kubernetes, hosts, and cloud services threats, along with actualising eBPF or kernel modules in time.
- Definition of malicious behavior (pre-loaded set included; falcoctl to update) as a set of rules that are customizable and extensible.
- It is normally coupled with SIEM, data lakes, Prometheus, and cloud integrations (e.g., AWS CloudTrail, GitHub).
- Interaction Lightweight user space CLI (falco), and Helm to be deployed with ease to Kubernetes.
- Open-source (CNCF project) is free of cost, core, x64/ARM compatible, GKE/EKS/AKS compatible.
Pros:
- Real-time threat detection
- Kubernetes-native
- Highly customizable rules
Cons:
- Not for image scanning
- Requires tuning (rules)
- Can generate noisy alerts
Pricing :
- Falco has created an open and free core
5. Dockle

Website:https://github.com/goodwithtech/dockle.
Dockle is a free open-source container image linter that helps in improving the safety of container images built by scanning constructed images and checking them against vulnerabilities, misconfigurations, and best practices like CIS Docker Benchmarks. It is written in Go and does not require any Dockerfile linters (like Hadolint) to scan image file systems and image layers to identify a problem: root user, sensitive files, empty passwords, or malicious permissions that might not be evident in the source code. It is also portable, and it can be applied in CI/CD pipelines using a few CLI instructions.
Key Features
- Identifies security threats like root users, a lack of health checks, and confidential files on constructed images.
- Imposes the compliance of the CIS Docker Benchmark of hardened, production-ready containers.
- Very basic CLI: scan images with zero configuration by giving the name of the image.
- Offers five severity levels, including PASS, INFO, NOTICE, WARNING, and FATAL, L and remediation advice.
- Supports inclusion in CI/CD pipelines with other tools such as Trivy or Clair to validate after building.
Pros:
- Simple and fast
- Focus on best practices (CIS benchmarks)
- Easy CLI usage
Cons:
- Limited to misconfigurations
- No deep vulnerability scanning
- Needs pairing with other tools
Pricing
- As an open-source application, Dockle is fully free with no charges or subscriptions.
6. Syft
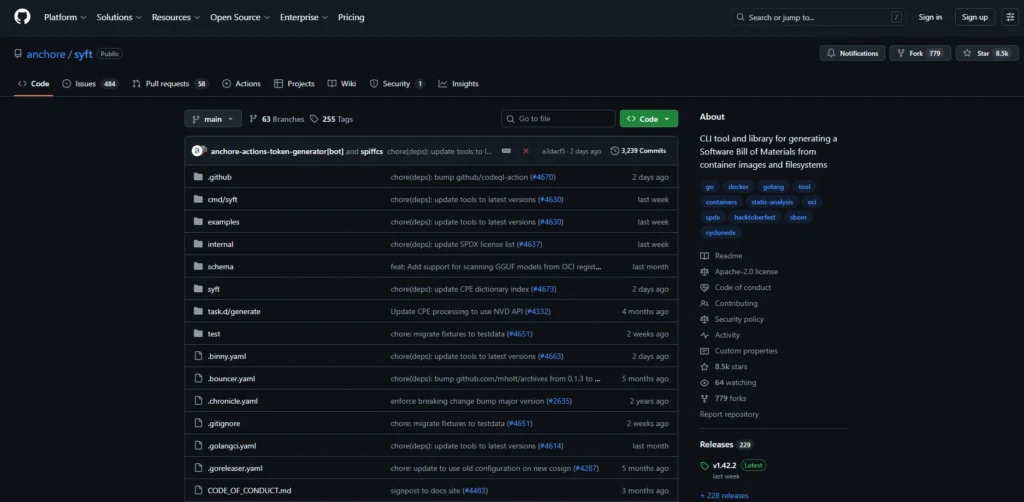
Website:https://github.com/anchore/syft
Syft is a CLI that is open-source and is used by Anchore to generate detailed Software Bills of Materials (SBOMs) based on container images, filesystems, directories, and code projects that do not run any code in them. container scanning tools It also recognizes and indexes software packages like packages (e.g., Alpine APK, Debian DEB, RPM, libraries, and binaries and dependencies of such languages as Go, Python, Java, and JavaScript to produce standard outputs to vulnerability analysis, license compliance, and security auditing in CI/CD pipelines.
Key Features
- Generates SBOMs in different formats, CycloneDX (JSON/XML), SPDX (JSON/tag-value), Syft JSON/table/text, and templates.
- Accepts many different sources , Docker/Podman daemons, OCI archives/directories, Singularity (SIF), registries, local files/directories.
- Identification of packages on 20+ ecosystems, including binaries that lack package manifests, multi-architecture (amd64, arm64).
- Options: Skip paths, scope layers (squashed/ all/deep), parallelism, verbosity, and external source enrichment.
- Companies like Grype can be helped with vulnerability scanning; CLI commands help with attest, cataloging, and format conversion.
Pros:
- Excellent SBOM generation
- Supports many ecosystems
- Lightweight and fast
Cons:
- No vulnerability scanning
- CLI-only
- Needs integration with other tools
Pricing
- Syft is an open source software and has no paid levels or licensing fees.
7. OSV Scanner

Website: https://osv.dev/
OSV-Scanner is an open-source vulnerability scanner that is a tool developed by Google to detect known security vulnerabilities in software dependencies or a container image by cross-checking package metadata and the OSV.dev vulnerability database. It helps scan other artifacts, including lockfiles, SBOMs, and container layers, without executing code, provides layer-sensitive analysis of containers to determine where vulnerabilities are introduced into containers, offers remediation recommendations, and provides the ability to filter.
Key Features
- Container image scanning that detects vulnerabilities in single image layers and base images.
- Lots of ecosystems are supported, e.g., OS packages, Go, Java, Python, npm, among others, via OSV.dev database.
- CLI-based and produce output in the form of a summarized table, JSON, and HTML reports, and serve a local web on detailed views.
- Image name scanning (with Docker/Podman) or no container runtime scanning of .tar archives.
- sort by severity, relevance, or custom profiles and show fixes where available.
- CI/CD pipeline support and GitHub automobile security check pipelines.
Pros:
- Backed by Google (OSV database)
- Accurate dependency scanning
- Supports multiple ecosystems
Cons:
- Limited features vs full platforms
- CLI-based
- Smaller ecosystem support than some competitors
Pricing:
- OSV-Scanner is free of charge, and is open-source, and has no paid levels.
8. Dive
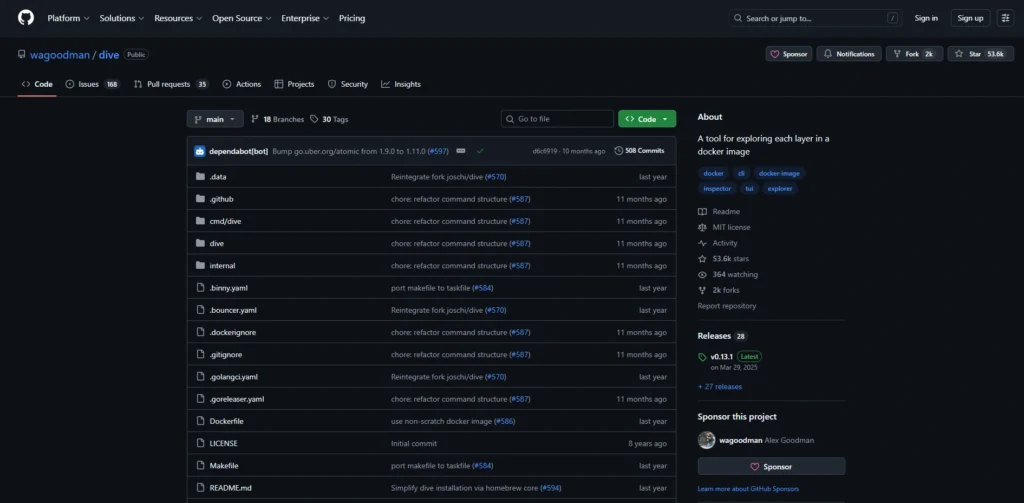
Website:https://github.com/wagoodman/dive
Dive (also Dive Scanner) is a free CLI utility that can be applied to explore and examine Docker and OCI container images and layers in detail. It may assist the developers to see what each layer contains, locate changes such as new, edited, or deleted files, container scanning tools and plan the amount of waste space to execute image size and performance when executing the CI/CD pipeline. It has a terminal-based UI (TUI) and can be used to perform swift analysis, construct images, and integrate CI to perform automated checks, which is useful in the optimization of containers instead of vulnerability scanning..
Key Features
- Divides the contents of Docker/OCI images by layer, displaying merged earlier layers with a selection.
- Show changes (added, modified, removed) of files per layer or aggregated.
- Calculate the image efficiency score and wastage due to duplicates or redundant files.
- Enables building of direct images and analysis with the dive build command.
- CI mode (CI=true) of pass/fail checks by configurable thresholds, such as efficiency >95% or wasted space <20MB.
- Various sources: Docker daemon (default), Podman, docker-archive tar files.
- TUI is based on the keyboard, filtering, directory collapse, and view toggles.
Pros:
- Visualizes image layers
- Helps optimize image size
- Easy to use TUI
Cons:
- Not a security scanner
- No vulnerability detection
- Limited to analysis only
Pricing:
- Dive is entirely open-source and is under the MIT license.
9. Kube-bench
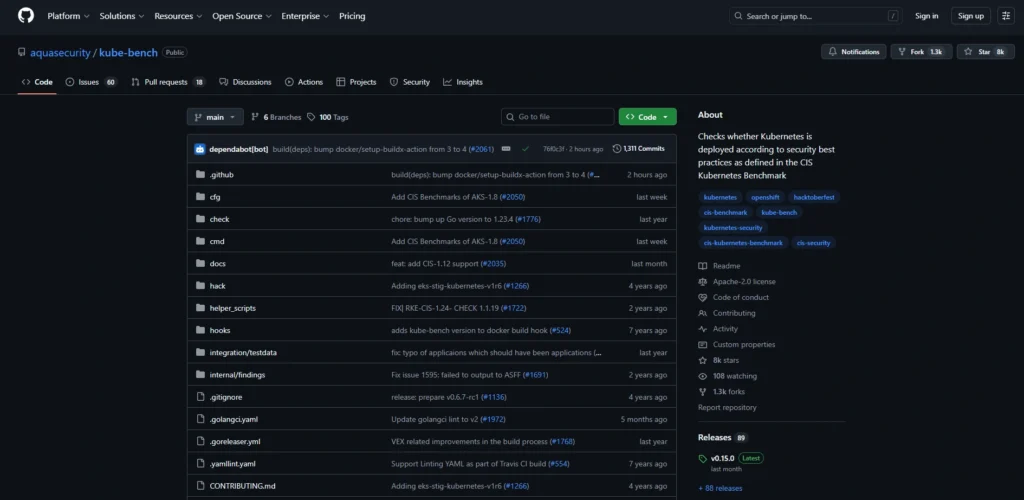
Website:https://github.com/aquasecurity/kube-bench
Kube-bench is an open-source tool designed by Aqua Security to test the security of a deployed Kubernetes cluster by running automated tests against the CIS Kubernetes Benchmark to determine whether there are misconfigurations in control plane components, nodes, and policies using file checks, command executions, and flag checks. It is configured by default as a container (e.g., using either Kubernetes Job or DaemonSet) and results in the form of text, JSON, or JUnit, which are easily integrable into CI/CD pipelines or dashboards.
Key Features
- Make a comparison between Kubernetes configurations and the CIS Benchmark of control plane (api server, etcd, scheduler), nodes (kubelet, kube- proxy), policies,s and networking.
- Several output formats,s like human-readable text, JSON, and JUnit, in the CI tool and reporting.
- Autodetermines Kubernetes version and node role (master/worker) to load appropriate benchmark rules.
- Runs in container mode and has privileged process and file checks.
- Tests written in YAML can be modified with a new CIS benchmark, or can be modified with custom rules in modules, and can be easily modified.
Pros:
- CIS benchmark compliance
- Kubernetes-focused
- Easy to run in clusters
Cons:
- Only checks configs
- No vulnerability scanning
- Limited scope
Pricing
- Kube-bench is an open source (under Apache-2.0) that is free of charge, and no paid levels or subscriptions are available.
10. Snyk Container
Website: https://snyk.io/
Anchore Engine is a container image scanning engine that is open-source and offers in-depth inspection, source vulnerability analysis, and policy enforcement of containerized applications. The basis of Anchore Enterprise is a trading platform with a more advanced mechanism, such as a user interface, scalable workflows, and professional DevSecOps integrations that allow security scanning, SBOM creation, and compliance checking of CI/CD pipelines, registries, and integration with workflow management platforms to streamline automated security and policy enforcement.
Key Features
- Pkg OS packages (dpkg, rpm, apk), application manifests, and unmanaged software such as Node.js and OpenJDK using file fingerprinting.
- Detects vulnerabilities by severity level, CVE detail,s and remediation recommendations without running the container.
- Provides integrations with container registries (Docker Hub, etc.), Kubernetes, CI/CD, and periodical scans of emerging vulnerabilities.
- Advises on image upgrades on the base image and does scanning of licenses in the wider Snyk packages.
- Provision of round-the-clock monitoring and notifications in Slack, Jira, or email after deployment.
Pros:
- Developer-friendly UI
- Strong CI/CD & IDE integration
- Good vulnerability database
Cons:
- Expensive pricing
- Limited free tier
- Slower for large scans
Pricing
- Snyk has a Free-plan that includes limited tests (100 Container tests/month, unlimited developers)
- Team (approximately $2598/dev/year) plans (unlimited scans of Containers) as well as higher levels, such as Ignite and Enterprise pricing.
11. Aqua Security (Trivy Enterprise)
Website:https://www.aquasec.com/products/trivy/
Trivy Enterprise is a commercial product by Aqua Security that is based on the popular Trivy vulnerability scanner but specifically tailored to high-performance scanning of containers in the enterprise. It was developed by Aqua Security and builds on the power of the core Trivy with scalable cloud-based code scanning of container images, registries, Kubernetes clusters, IaC configuration (such as Dockerfiles and Terraform), filesystems, Git repositories, and dynamically analyzes threats through sandboxing.
Key Features:
- Images Scans container images, Windows containers, private/public registries (with ECR, GCR, ACR support), and caching of layers using scalable cloud infrastructure.
- Identifies vulnerabilities (CVEs), malware, misconfigurations, and exposed secrets, RBAC problems, and checks SAST code.
- The software is compatible with Kubernetes cluster scanning, IaC (Terraform, CloudFormation), Git repos, VMs, and SBOM/license generation.
- Business extras such as dynamic threat analysis (DTA/sandboxing), a wider scope of threats compared to OSS Trivy, as well as a CI/CD pipeline offering.
Pros:
- Scalable enterprise solution
- Advanced security features
- Broad coverage (IaC, cloud, runtime)
Cons:
- Paid (no public pricing)
- Complex setup
- Overkill for small teams
Pricing
Pricing of Trivy Enterprise is not publicly available and should be contacted through the Aqua Security sales in order to get a custom quote based on usage, scale, and features; it is priced higher to project itself as an upgrade to the free open-source edition.
12. Wiz
Website: https://www.wiz.io/.
Wiz Scanner is a container scanner offered as part of the Wiz cloud security platform and is utilized to identify vulnerabilities, malware, secrets, and misconfigurations in container images, either in CI/CD pipelines or when running. container scanning tools It fits well with registries such as Docker Hub, ECR, and others, and scans image layers, packages, libraries, and runtime artifacts with agentless scanning via the Wiz CLI to analyze prioritized risks with context such as exploitability scores. This helps DevSecOps teams to address problems proactively and not disrupt the workflow.
Key Features
- Vulnerabilities, secrets, and compliance issues. Scans images in registries (Docker Hub, ECR, GCR, JFrog, ACR, Harbor, Quay).
- Enables orchestration and ingestion patterns of automated pipeline integration (e.g., Harness STO).
- Auto identifies targets and variants (image name/tag) and has configurable fail-on-severity (Critical, High, Medium).
- Delivers correlated and deduplicated results with trends and workspace-specific scanning.
- Operation using CLI agents (without an agent) with support of Docker-in-Docker and local OCI archives.
Pros:
- Agentless scanning
- Strong cloud-native security
- Context-based risk prioritization
Cons:
- Very expensive
- Requires cloud integration
- Not ideal for small teams
Pricing:
- Wiz uses the subscription price depending on the cloud’s workload volume and is usually effective for mid-sized teams at approximately $5,000 -10000 per month (custom quotes via sales).
Comparison Table
| Tool Name | Type | Key Strength | Best For | CI/CD Integration | Pricing |
|---|---|---|---|---|---|
| Trivy | Open Source | All-in-one scanning (vulnerabilities, secrets, SBOM) | Developers & DevSecOps teams | Yes | Free |
| Clair | Open Source | Deep layer-based vulnerability analysis | Container registries | Yes | Free + Paid plans |
| Anchore Engine / Enterprise | Open Source + Enterprise | Policy enforcement & compliance | Large enterprises | Yes | Custom pricing |
| Falco | Open Source | Real-time runtime threat detection | Kubernetes security | Yes | Free |
| Dockle | Open Source | Container best practices & misconfig checks | Lightweight security checks | Yes | Free |
| Syft | Open Source | SBOM generation | Compliance & auditing | Yes | Free |
| OSV Scanner | Open Source | Dependency vulnerability scanning | Developers & open-source projects | Yes | Free |
| Dive | Open Source | Image layer analysis & optimization | Image performance tuning | Limited | Free |
| Kube-bench | Open Source | Kubernetes CIS benchmark checks | Kubernetes admins | Yes | Free |
| Snyk Container | Commercial | Developer-friendly security platform | Teams needing UI & automation | Yes | Free + Paid |
| Aqua Security (Trivy Enterprise) | Enterprise | Advanced cloud-native security | Large-scale organizations | Yes | Custom pricing |
| Wiz | Enterprise | Agentless cloud security & risk prioritization | Enterprise cloud environments | Yes | Paid (custom) |
Conclusion
DevOps teams have the authority to find vulnerabilities, misconfigurations, and secrets at the start of the CI/CD cycle thanks to container checking software like Trivy, Clair, Snyk, and others, and release their products safely and safely without being held up in rush-hour traffic: the responsible Delhi Metro guard deterring accidents before they occur.
Container Scanning Tools Should you go with a fast start of free open-source, like Dockle and Syft, or a scalable solution, like Aqua Security and Wiz, both of which will enable you to improve your security posture, minimize downtime, and ship containers with confidence. You can start the one that fits your stack now, and can transform your possible nightmares into flawless superhero triumphs.
FAQs
Q.1 What Does A Container Scanning Platform Mean?
In order to provide protection to DevOps pipelines, a scan of container images and runtime environments is performed with the help of container scanning tools and checked to reveal vulnerabilities, misconfigurations, secrets, and malware. They are being combined with CI/CD, such as Jenkins or GitHub Actions.
Q.2 Why Is It Necessary To Scan Containers?
The containers usually use old base images that are known to contain CVEs that create breaches whenever they are built. Early scanning would identify breaches and require SBOM requirements and 70-90% minimization of attack surfaces in applications built in the cloud-native context.
Q.3 Why Is It That Clair And Trivy Are Different?
Trivy is a rapid scanner (no daemon required) that can be characterized as all-in-one (vuln, secrets, misconfigs), yet it is most suited to CI, and is also daemon-based, where it is capable of scanning registries via APIs (but its local mode is slower).
Q.4 Which Tool Can Best Be Used With Kubernetes?
Aqua Security is the best K8s run time protection and drift detector offering, sidecar and runtime scanners Trivy or Sysdig, and behavior anomaly detector Falco.
Q.5 What Are The Ways To Implement Scanning Into CI/CD?
Install Plugins: trivy image myapp:kllatest in GitLab CI or snyk container test with Snyk in GitHub actions; configure fail-thresholds on the highest/critical CVEs on the automated gates.

